|
An Epidemic
of Malware and Ways to Protect Yourself
by Basil Irwin
12/19/2008
The Malware Problem
Malware infections (viruses, Trojans, etc.) are
drastically on the rise right now and are having devastating impacts on Windows
PCs, generally rendering them unusable until the infections are removed. Such
removal can sometimes be quite difficult, and often the OS is left damaged and/or
deliberately vulnerable to subsequent infection, even when the malware is
successfully removed.
Unfortunately, current malware infections have become almost
impossible to prevent, as they are designed to trick you into
installing them and then
hide themselves in such a way that most protection software can
not see
them or remove them.
Unfortunately, anytime you click a link on a web page or in an email, malware
could be surreptitiously installed. Fortunately, this is not a problem to worry about on corporate web sites like ebay.com, amazon.com, craigslist.org, yahoo.com, microsoft.com, msn.com,
hotmail.com, aol.com, cnet.com, download.com, apple.com, and millions of other main stream web
sites.
The malware problem mainly arises from fake web sites and from social networking
web sites in which people can post their own content, such as facebook.com,
myspace.com, and many others. Many of the fake web sites are porn sites. Legitimate
porn sites just want to make money and have no interest in infecting your computer.
However, fake porn web sites are like all other fake web sites, they just want to wreak
havoc on your computer. Unfortunately, most porn sites are fake.
Another common means of infection is via user-initiated software downloads,
particularly antivirus programs, most of which are fake. With only a
handful of exceptions, free antivirus and free "cleaner" programs are
themselves malware. Further, most software download sites are fakes. A few
of the legitimate software download sites are download.com, majorgeeks.com, tucows.com,
pcmag.com, pcworld.com, brothersoft.com and snapfiles.com, as well as thousands of vendor-specific web sites. My advice is to avoid downloading
software from sites other than the listed ones or vendor-specific sites, unless you know with 100%
certainty that the site is legitimate and the software you are downloading is
legitimate.
During routine web surfing, however, infection usually occurs via trickery, using
popup windows that look legitimate and which scare you into clicking on a
button that does something entirely different than what the web pages says the
button does, namely installing malware instead of the indicated operation.
These popup ploys are too numerous to describe, but typically indicate that a
codec or flash viewer or some other piece of software must be installed to
continue, or they indicate that a malware infection has occurred (it hasn't) and
that you must take the indicated action to protect yourself (if you do, you'll actually
be installing the malware).
Unfortunately, a tiny few of
these installation requests are legitimate, but the best course of action
if you are not 100% sure of what to do when such a popup occurs, is to
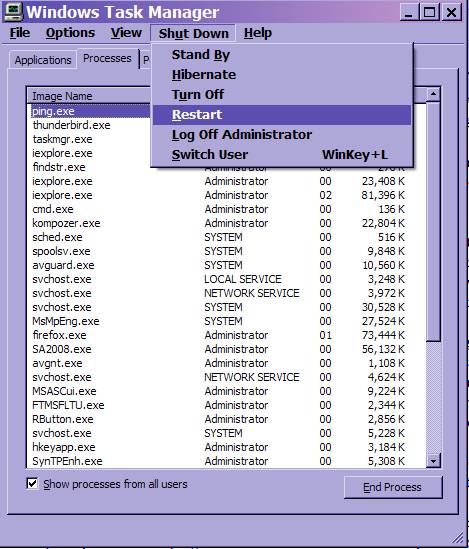
gracefully shut down your system and restart it by pressing Ctrl + Alt + Del at
the same time so as to activate the Windows Task Manager. When the Task
Manager appears, you can restart the system by clicking the “Shut Down” tab and
selecting “Restart” as shown below:
By the way, if you have accepted my recommendation for having Avira
Antivir installed, the only legitimate malware warning message
that you will receive looks like the following popup that occurs when Antivir
Guard has detected malware:
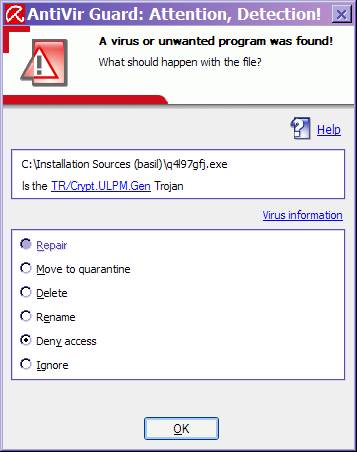
(By the way, one should
always select “Move to quarantine” as the action to take if the AntiVir Guard
screen appears.)
A Good Way to Fix the Malware Problem
However, even with all of
these precautions, malware can still slip in. For example, a legitimate web site
can be unknowingly compromised and subsequently distribute malware
until its operator detects the compromise and repairs it.
So, I've finally concluded
that the only way of really being safe from infection is to work from a user
login id that is set up as being a "limited account" login id, which
is explained in the following paragraph.
Windows provides two levels
of privilege for login ids: 1.) "administrator" privilege, in
which the user and the user's programs are allowed to perform all possible
system modification or configuration operations (even dangerous or malicious
ones), and 2.) "limited account" privilege, in which no system
modification or configuration operations are allowed, though performing most ordinary
operations are allowed, including surfing the web, reading email, using
Microsoft Office and almost all other applications. But because "Limited
account" login ids are inherently unable to install any software at all,
malware installation is prevented as well.
For
several years, I've
established limited account login ids for clients with children or
teens
because they are extremely vulnerable to being tricked into installing
malware,
and these limited accounts have worked quite well. In fact, in some
cases, their parents have also requested a limited account login id as
a safety precaution.
The adults use the limited account for ordinary work but can
temporarily login
to an administrative account if they need to install a new program,
etc. This
strategy has worked very well also.
So, I’ve recently concluded
that the best strategy for many people is to have an administrative login
id that is used only for administrative work, and also to have a limited account login id used for
all ordinary, everyday activity. In particular, if you tend to surf web sites
outside of the main stream or are very uncertain about which action-requesting
popups are legitimate, or you just want to be super safe, you might want to consider the dual login id strategy.
For brand new systems, it's fairly
easy to establish both limited and administrative login ids. For older systems,
conversion can be a little more involved, as usually the best thing to do is to
add a new administrative account and change the existing login id to a limited
account. However, the main complication for the conversion method is that many
system files continue to be "owned" by the converted login id, and
ownership of all of these files must be changed to fully secure the system.
Some Parting Advice
It is always essential that
Automatic Updates be "On", and that a good antivirus program such as
Avira Antivir be active and automatically maintain its signature
database. An
antispyware program is also a good idea. I recommend Windows Defender.
Antivir and Windows Defender are both free, lightweight,
unobtrusive, and update for free.
Furthermore, I recommend
Firefox version 2.0.0.18 instead of Internet Explorer 7 as your default
browser, since Firefox is less prone to the numerous security breaches that
continue to plague IE7. However, I don't currently recommend Firefox 3.0 as I
don't think it is stable yet. Also, a bit of tuning along with a handful of
"add-ons" can make Firefox browsing even better than it is right out
of the box, paticularly add-ons that stop advertising and stop automatic playing of flash clips.
And lastly, never click
on a web link in any email unless you are 100% certain that the link is safe. If you must visit the link, copy the link into the
clipboard and then paste the link into the address bar of your browser, at
which point you can look at where the link is really going, and decide whether the
destination looks legitimate.
Basil Irwin
www.reliancepc.com
303-774-1526
(Please feel free to forward this email to others. Also, this newsletter and all previous newsletters are archived at: www.reliancepc.com/menu/newsletters. Oh, and remember what I said about clicking on links in email!)
|
 )
)